ID authentication software
IDScan.net document authentication software puts every ID through more than 400 AI-powered security checks – many of them proprietary – to help catch fake IDs and prevent ID fraud.
95% accurate
Fake ID detection
500M
Training scans
9,700
Global documents supported

 Windowpane Passed
Windowpane Passed  Microprint 600dpi Passed
Microprint 600dpi Passed ID AUTHENTICATION SOFTWARE
How we authenticate identity documents
- Ultraviolet light
- Infrared light
- Front / back crossmatch
- Barcode security
- Security feature checks
- RFID checks
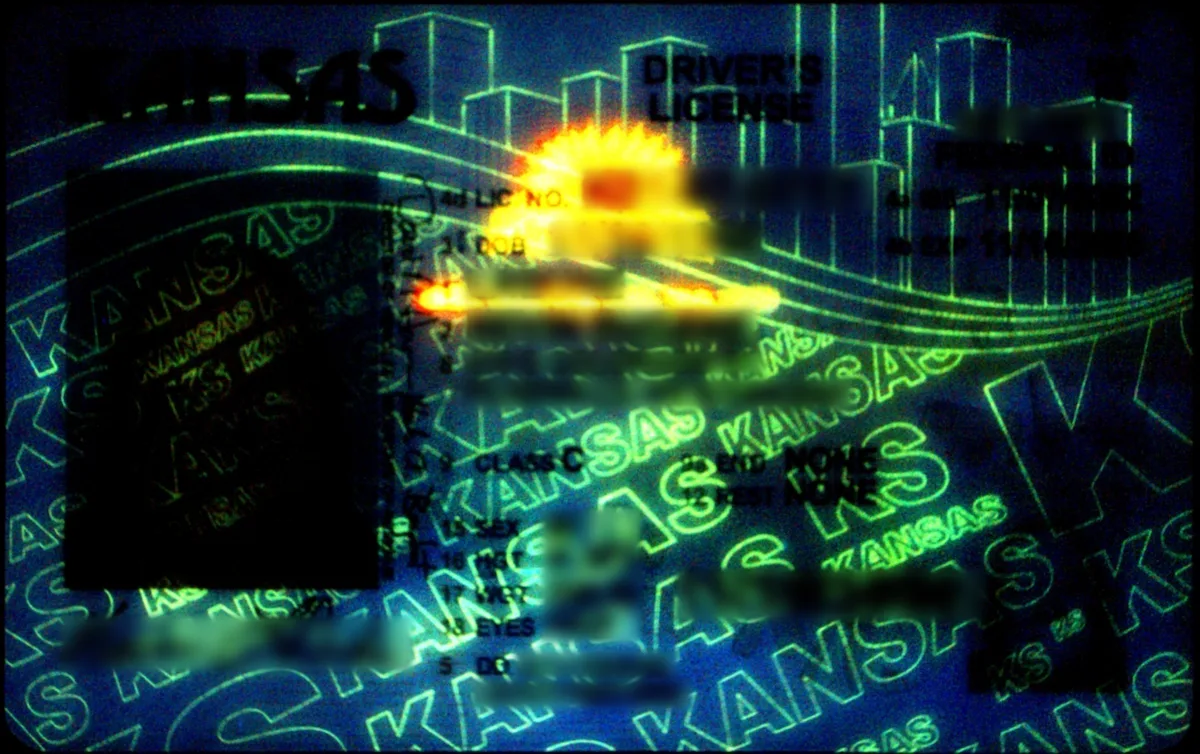
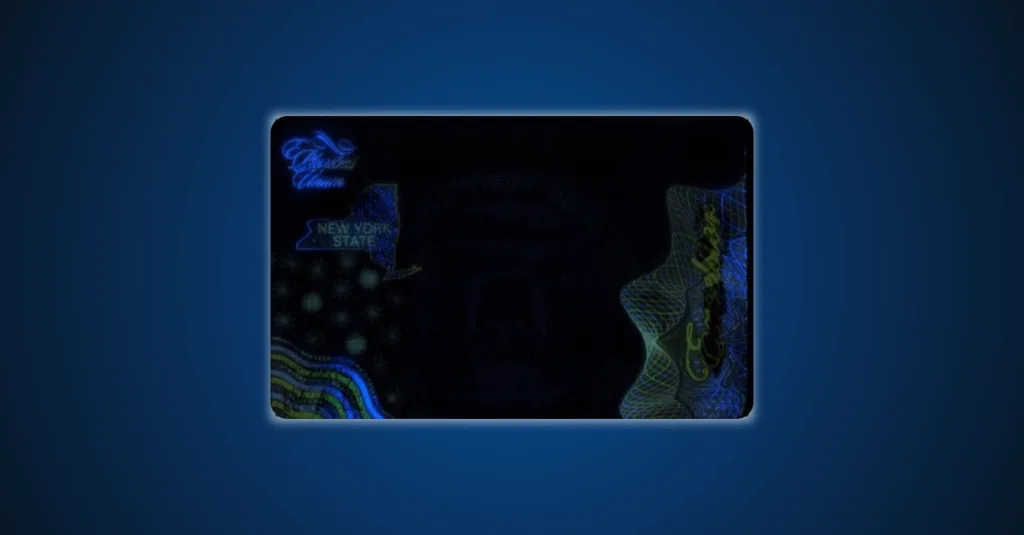
UV ID scanning
Nearly all ID formats contain symbols or text that are only visible under ultraviolet (UV) light. This is commonly why bouncers use a small, UV light when checking IDs.
Our software reviews scans made under ultraviolet illumination to check for the presence of UV elements or response. We use artificial intelligence to go much further than the bouncer’s flashlight, comparing the marks and elements seen under ultraviolet light to the template for that ID’s jurisdictional format.

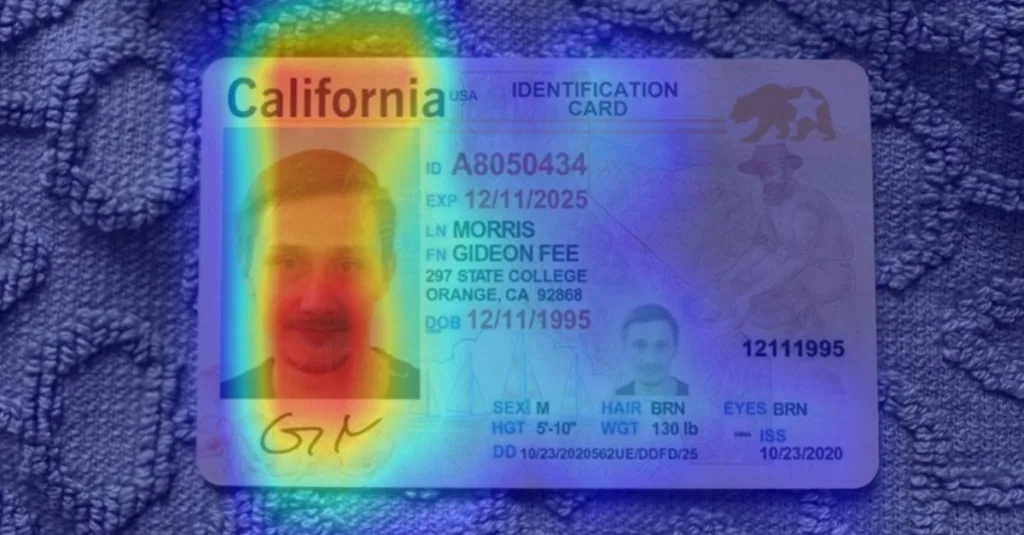
Infrared ID scanning
Infrared light has a wavelength longer than visible light, so it provides a different perspective on the visual information stored on the ID. Infrared elements may include data such as name, ID number, expiration dates, photo reprint, or special lines and markings.
Our software checks for the presence of expected marks under infrared light conditions, or if infrared light reveals marks that are not expected to appear on that jurisdictional format.
The infrared light check is critical to ensure the document’s authenticity.

Using OCR to compare the front and back of the ID
Our instant barcode parsing reads and validates the data stored in the 2D barcode of the ID. Then our software uses optical character recognition (OCR) to read the text on the front of the document.
Our software instantly compares the two sets of data, catching reuse of legitimate IDs, data scrubs, and tampered IDs.
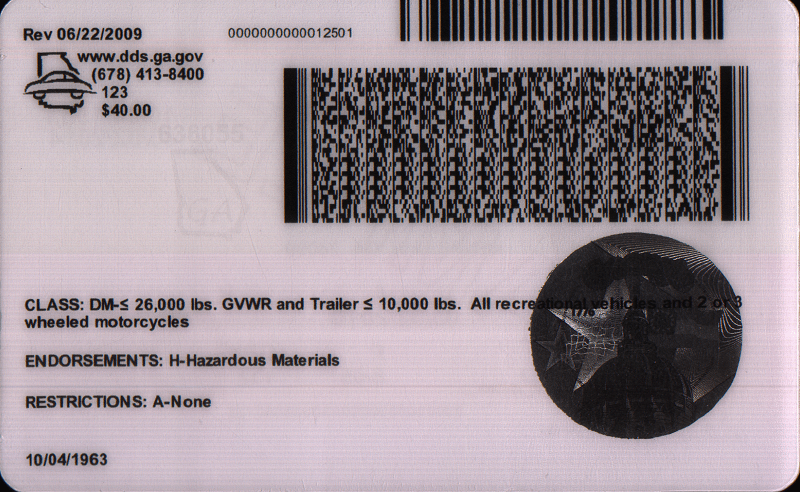
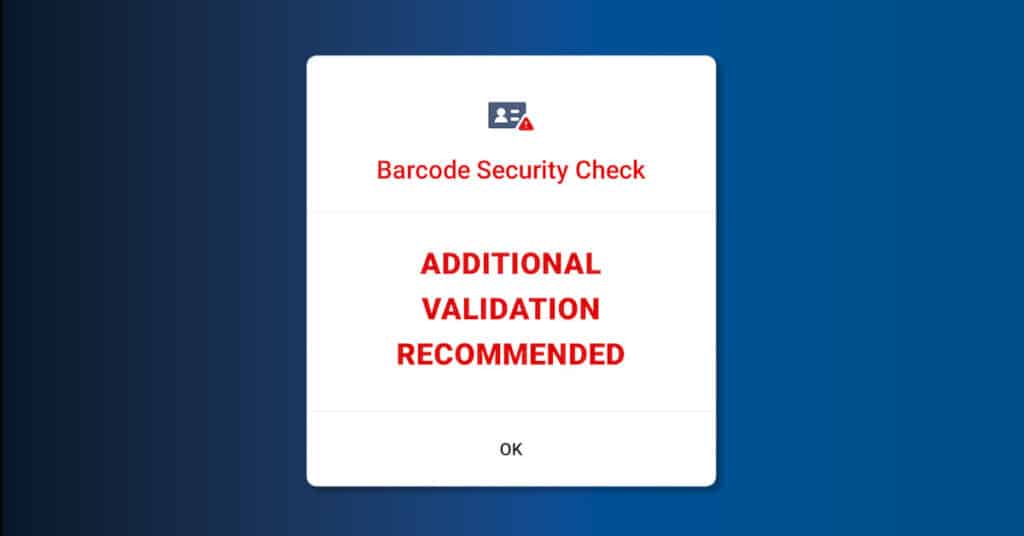
Barcode syntax check
The 2D barcode (PDF417) contains all the data on the front of the ID (first name, last name, DOB, etc) as well as embedded security features unique to every jurisdiction. Our software has cracked the code on these security features after scanning more than 500,00,00 IDs through our machine learning models.
This deep expertise allows our software to easily identify IDs which lack the correct barcode formatting or are missing hidden security features and easter eggs in the PDF417.



Pixel-level review of security features
Every year, issuing authorities launch new ID formats with additional security features. These are intended to make the IDs harder to forge, and more difficult to alter by tampering.
These security features include windowpanes, micro-prints, holograms or lenticular prints, and other proprietary features which may not even be visible to the naked eye.



RFID crossmatch (on select documents
All passports and some ID cards, contain an RFID chip. When paired with a forensic document scanner that is capable of reading RFID, our software can read the fields stored in the RFID chip and compare them to the text fields, and encrypted fields on the document.
HOW TO IMPLEMENT
Desktop document authentication software
Connect an ID authentication capable document reader to a Windows computer and run powerful, rapid document authentication to confirm the legitimacy of documents in seconds.
Our rules engine allows for the most efficient workflow based on the document type, document series, issue date, and more. The software allows government and private entities to quickly verify customer credentials, stop fraud, and comply with stringent KYC requirements.
Authentication via SDK
Install on-premises document authentication with our lightweight .Net SDK, licensed from the cloud.
Authentication via API
Capture images on device and then send them to the cloud for rapid processing and analysis.
Authentication in our off-the-shelf software products
Our VeriScan identity platform offers easy-to-use ID authentication which sends results directly into our secure, visitor management and fraud prevention software.

VeriScan ID authentication pricing
In order to authenticate IDs, you will need to pair VeriScan ID Authentication with specialty hardware.
ID AUTHENTICATION
Why implement fake ID detection software
Our machine learning has been trained on millions of documents to detect the most fake IDs.
ID fraud prevention
Sophisticated, foreign-made fake IDs help organized criminals. and fraudsters impersonate legitimate customers.
Access management
Scan and authenticate IDs at the entrance to your facility to ensure the highest standards of safety on-site.
Compliance
KYC and AML checks are a part of most banking and lending workflows. Ensure their identity credential is legitimate before initiating key workflows.
Age verification
Today’s underage customers have access to realistic fake documents. Use ID authentication to stay compliant and keep minors out.
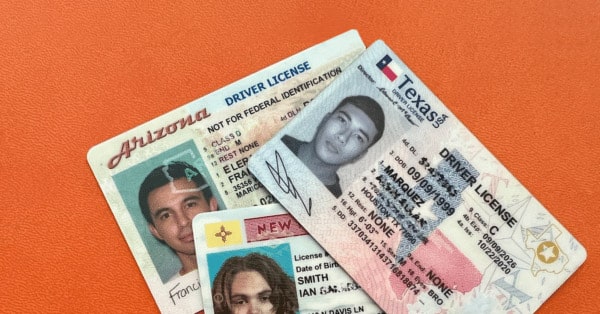
Best ID scanners for catching fakes
To catch fake IDs and perform document authentication you will need specialty hardware capable of multi-light scanning and checks against hologram and watermark libraries.
| ID scanner make/model | Thales CR5400 | Thales AT9000 | Thales AT10K | E-Seek M500 |
| Scanner type | Drop-in | Flatbed | Flatbed | Drop-in |
| Scans all North American IDs | ||||
| Scans global passport books | ||||
| Detect expired IDs | ||||
| Age verification (18+, 21+) | ||||
| 2D barcode security checks to catch anomalous PDF417 barcodes | ||||
| Optical character recognition (OCR) for front/back matching | ||||
| Ultraviolet, infrared light scanning | ||||
| Hologram, watermark check capable | ||||
| Capable of catching up to 95% of fake IDs | ||||
| RFID | ||||
| Near field communication (NFC) | ||||
| Image resolution | 300dpi | 400dpi | 550dpi | 600dpi |
| Power source | USB | External | External | External |
| Dimensions | 7″ x 4.25″ x 4.53″ | 7.5″ x 6.4″ 6.2″ | 7.4″ x 6.3″ x 2.6″ | 4.8″ x 5.7″ x 8.5″ |
| Weight | 2.2 lbs | 2.2 lbs | 2.4 lbs | 4.5 lbs |
| Time to authenticate (per ID) – may vary based on system speed | 7.19 seconds | 11.77 seconds | 10.09 seconds | 7.50 seconds |
| Manufacturing location | US / China | China | China | South Korea |
| Data Sheet | ||||
ID authentication must run on a computer with at least 32-bit or 64-bit processing capabilities with sufficient bandwidth to perform the forensic document analysis needed at speed.
Become an ID authentication expert
Learn more about how we use machine learning to deeply analyze identity documents to catch 95% of fake IDs
AI-created fake ID images – can they fool ID verification technology?
On overview of the emerging ID security feature – the photo windowpane – and which states have implemented it.
Holograms & Lenticular Prints on US IDs
Learn about holograms, ultraviolet markings, and lenticular printing on North American IDs and drivers licenses.
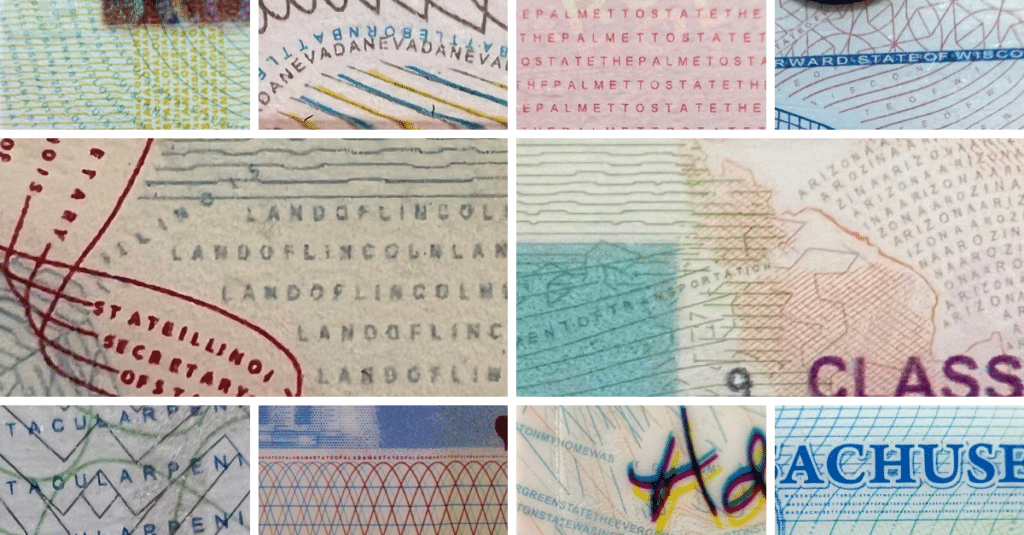
Which states include microprint as an ID security feature
An overview of all North American IDs and how they use microprint to protect against forgeries.
Which states include windowpanes as an ID security feature
On overview of the emerging ID security feature – the photo windowpane – and which states have implemented it.
What to do when you catch a fake ID
See our 50-stare guide to laws and regulations for confiscating (or not) a presented fake ID

Anatomy of a drivers license
Learn all about the security features and design elements present on US drivers licenses
5 reasons a legitimate ID might be flagged as fake
Several key reasons that ID authentication software may fail an ID, even though its a legitimate document.
Different types of symbologies
PDF417, MRZ, 1D barcode, and QR code are all symbologies which can contain ID data.
ID authentication FAQ
How accurate is your ID authentication software?
We regularly achieve accuracy at detecting more than 95% of fake IDs. However, fraudsters are tricky and they are always adapting. Fake IDs become more and more sophisticated each year. There will always be exceptional fakes that cannot be detected by any software (or the human eye). Our software is Adaptive AI, and we continuously train three distinct neural networks to improve our rate of fake detection.
Additionally, we go above and beyond to prevent false positives, because we know the last thing our customers want is to turn away a legitimate patron, or accuse an honest customer of using a fake ID. For this reason, we offer configurable strictness levels, which allow you to determine your own acceptable thresholds to best meet your business objectives.
Can fake ID scanner apps (iOS, Android) detect fake IDs?
Mobile apps can catch some percentage of fake IDs using 2D barcode security checks. 2D barcode security (sometimes called “ID validation”) performs a series of checks on the information on the 2D barcode. These checks are for fake ID “tells” such as mis-spellings, using incorrect abbreviations (ex. shortening Brown to “BWN” instead of “BRN”), size, and location of the barcode. Many low quality fakes cannot pass these barcode security checks, and so apps that read only the 2D barcode (mobile apps and ID scanning software running on a mobile device) can catch these.
However, we have compared the results of some of the most commonly used mobile apps which claim to verify age and detect fakes. They caught less than 35% of the fakes in our library, and some of the apps caught none at all.
What types of documents can be authenticated?
VeriScan is capable of authenticating documents, IDs, drivers licenses, and passports from around the world.
How much does ID authentication cost?
ID authentication is commonly purchased as VeriScan ID Authentication, which offers the full visitor management and age verification software suite in addition to ID authentication. It can also be used with our ParseLink product to rapidly authenticate iDs before sending the ID data into your existing software. You can view pricing on our pricing page.
What security features are commonly featured on IDs?
IDs commonly feature a variety of visual and embedded security features. Some of the visual features include holograms, lenticular prints, micro-perforations, microprint, and window panes.
Which ID scanners can perform authentication?
ID authentication requires ID scanning hardware that can perform UV, infrared, and white light scanning, front/back matching, and hologram and watermark library checks. We sell the following authentication-capable ID scanning hardware:
- Thales CR5400
- E-Seek M500 (best-in-class)
- Thales AT10K (IDs and passports)
- Thales AT9K (IDs and passports)
Because we know this sophisticated hardware can sometimes present a cost barrier, we sell open-box and certified refurbished scanners at a low price point.
What if a person simply uses another person’s legitimate ID?
ID authentication can only tell you whether a document is authentic. Face matching would be required to match the individual present to the ID photo. Usage of an ID that belongs to someone else is called a “false ID.”
How do you authenticate mobile drivers licenses?
Mobile drivers licenses (mDLs) have their security features embedded into the application itself, typically in the form of biometric access management (fingerprint, face ID). There is currently no ability (nor need) to authenticate a digital identity document.
How does document authentication differ from document verification?
Document authentication is a much deeper set of checks that involves analysis of all available security features on the identity document.
Is ID authentication required by law in certain industries?
Yes, there are certain industries and use cases that require document authentication in order to ensure that businesses are meeting the highest standards for compliance.






